Best Access Control Brand Reviews
Looking to buy access control? Read reviews of the best brands.

Alarms | ||
Cloud camera integration | ||
Cloud-based | ||
Data export | ||
Direct support | ||
Directory integrations | ||
Lockdown feature | ||
Native mobile access | ||
Public API | ||
Remote unlocks | ||
SAML SSO-enabled |
MicroStrategy Usher provides real-time physical access control with high visibility from a central location.
The facility management system can be integrated with two subcomponents:
The employee badge management system is compatible with multiple existing physical access control systems from other vendors. It is based on multi-factor authentication, which enables employees easy access to company premises, offices, factories and other physical barriers.
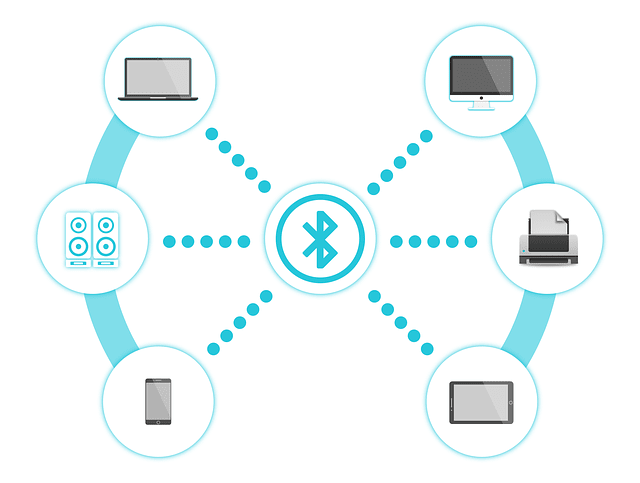
To open doors, employees can choose between Bluetooth proximity authentication and digital key tapping. Additional features of MicroStrategy Usher for employee badge management include push notifications, biometric access control, one-time passwords, time and geofencing identification, and face-to-face recognition.
The visitor badge management system is based on digital pass cards that solve many problems of lost, damaged or stolen access cards.
MicroStrategy Usher for visitor badges enables digital identification of the badge owner and time-designated digital badges. Such badges can be easily revoked. Since they implement encryption certificates with public and private keys, breaches are impossible. Digital badges come in several variants. Similar to the employee management system, visitors can use Bluetooth proximity, QR codes, biometric credentials, and one-time passcodes to access the building.
The entire concept of MicroStrategy Usher is based on a mobile access control to avoid the typical issues of other authentication devices, such as cards or fobs.
Managers use the Usher platform to grant and revoke user access. Users get access with smartphone digital keys, NFC, and Bluetooth options, but may also need to authenticate additionally with biometrics or by using more than one of the above technologies. The integration with other productivity and analytics apps by MicroStrategy makes Usher an effective business management tool, which business owners can use to communicate and collaborate globally.
Businesses can choose between several Usher mobile configurations available as license key models:
Users must own the Usher Security mobile app on their smartphones to be able to identify with the digital badges.
This MicroStrategy Usher review shows that its products and services are best suited for international businesses with multiple satellite offices that require continuous support with consulting services and have the need for big data management and analytics support.
MicroStrategy Usher is software-based, which means that it doesn’t include additional components of physical access control systems (PACS). Since it can be integrated with vendors like Lenel or Honeywell, it may work best with access control systems that already implement one of these systems as their access control solutions.
Best Access Control Brand Reviews
Looking to buy access control? Read reviews of the best brands.
Enable cookies to help us improve your experience.
We use cookies to enchance your experience and for marketing purposes. By clicking ‘accept’, you agree to this use.