Legacy access control systems have dominated workplaces since the 1960s. Then keypad security controls were employed to restrict access and reduce the overall amount of physical keys that needed to be duplicated or replaced. While keypad access control solutions were the beginning, they paved the way for magstripe cards, RFID, and mobile unlocking capabilities.
As technology advances and the modern office evolves, many workplaces are feeling the pains of their legacy solutions. Here we’ll explore the advantages of migrating to a cloud-based solution, review potential challenges, and identify system migration considerations.
Topic 1: Access Control Migration Advantages
More and more businesses have made the decision to migrate their physical access control solution to the cloud. While the motivations vary by company, we’ve broken down the most common advantages businesses experience from a migration.
Cost-effective
Legacy systems are expensive to maintain, operate, and upgrade. As solution components become dated, replacement parts become increasingly difficult to locate, if they are even supported.
Continuous updates
Scheduling downtime to apply security patches and updates doesn’t have to keep IT teams up at night anymore. With a cloud-based system, the provider automatically updates your access control software, giving you the latest functionalities while ensuring security compliance.
Enhanced security
As a result of periodic maintenance, updates, and security patches, legacy systems are often more open to security breaches. Cloud-based systems, purchased from established companies, are monitored, updated, and supported 24-7.
Dedicated support
Cloud-based access control systems employ dedicated support teams with a deep understanding of your solution. They can advise you on how best to resolve minor issues like removing users permissions or help you handle major system failings from the comfort of your office or home.
Flexible credentials
In addition to supporting traditional cards and fobs, cloud-based solutions employ technology to handle multiple communication protocols. Cloud-based credential enrollment allows administrators to manage user permissions from anywhere at any time.
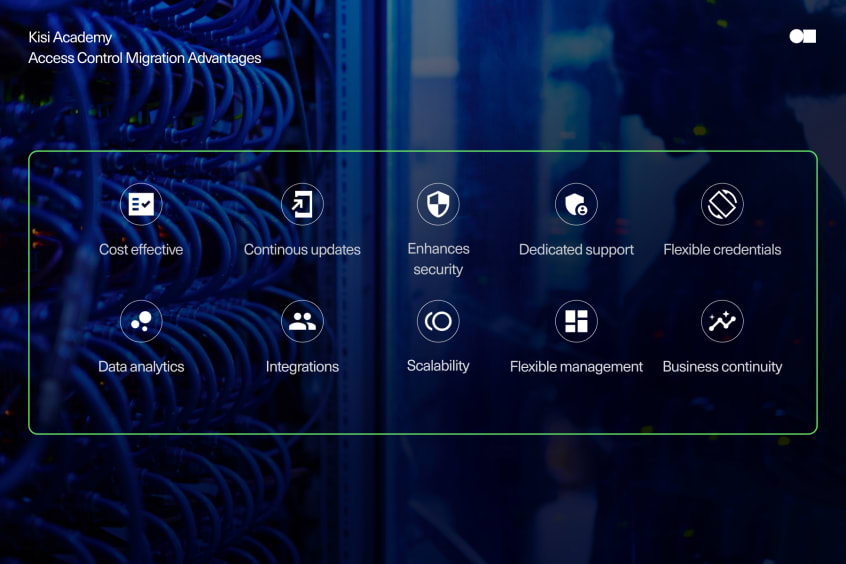
Data analytics
Understanding how your space is utilized, identifying usage trends, or investigating potential incidents is made easy for cloud-based administrators. Security audits and event filtering is accessible from the provider’s web dashboard.
Integrations
Cloud-based solutions often come with a portfolio of supported integration partners to help end users get the most out of their access control system. Integrations are most often used to provision (or revoke) credentials, review camera footage related to specific events, or monetize a space.
Scalability
Securing additional doors or locations? With a cloud-based solution, scaling is easier and less costly than with an on-premise solution. On-premise solutions require dedicated server space and adequate power at every installation location. With cloud-based solutions, cabling and wiring are limited and servers are hosted by the provider eliminating that cost completely.
Flexible management
Running multiple facilities from a single location has never been easier than with a cloud-based solution. Legacy systems require the administrator or technician to make changes or update system permissions while connected to the server locally on-site. For multi-national and global organizations, this could mean several people are responsible for ensuring the system is running in accordance with the organization’s security policy. Delays in accessing event history or revoking user access could result in losses, damages, or unauthorized access.
Business continuity
In the event of a natural disaster, server failure, or other catastrophic events you won't lose access to your system. Cloud-based solutions, like Kisi, are hosted on more than one server, offering better reliability and security than on-premise solutions.
Topic 2: Access Control Migration Challenges
Identifying the need to migrate is an important determination. Understanding common constraints and challenges of a migration before starting the journey will allow you to proactively address them. We will explore some of the more common migration challenges businesses face.

Upgrade cost
Upgrading from a legacy system to a cloud-based solution may feel like a significant investment, especially if your existing systems are performing adequately. Identifying a cloud-based solution provider compatible with your existing system hardware would allow you to significantly reduce your overall project cost.
Learning curve
Humans are creatures of habit. If a solution that worked before, such as door access, becomes more difficult or less intuitive, users will feel frustrated and voice their disapproval. Ensuring your users have a smooth transition is important for user confidence and happiness with the new system.
Solution proficiency
Selecting a solution that is user intuitive and simple to use will bolster the confidence of system administrators. Less intuitive solutions often require upskilling your current IT team or hiring new talent to get the most out of your system.
Unclear goal
With several cloud-based solutions to choose from, it is important you define your migration goals in advance. With a better understanding of what you are trying to accomplish, you can eliminate providers that will not meet your project objectives.
Topic 3: Access Control Migration Considerations
Clear objectives, thorough planning, and careful consideration are the prerequisites for a seamless access control migration. Before starting to plan your migration, let’s reflect on the considerations.

Software
Selecting a software solution that minimizes the impact on end users and administrators while delivering the functionality necessary to operate your business should be a primary consideration. Identifying a system that delivers on this front would be the least intrusive way to migrate from a legacy system.
Hardware
Determining if your current hardware would be suitable for migration depends on your goals. Upgrading to the cloud doesn’t have to mean replacing systems that work. Choosing a cloud-based solution that is compatible with your existing hardware will allow you to upgrade without putting down a small fortune. This is the time to weigh the convenience and familiarity of your current credentials against the security. If your credentials and readers are not encrypted, it would be a good time to reevaluate replacing existing readers.
Network and wiring
Latency and bandwidth are important considerations when assessing the network requirements of a cloud-based system. Explore the ability to reuse current wirings, like reader-to-panel, reader-to-interface module, controller wiring, interface module to controller, and I/O wiring to interface modules. Any additional wiring will contribute to the overall migration cost.
Power
Understand the power requirements for new hardware components. Is it 12V or 24V and AC or DC? Will it provide appropriate current for the new hardware pieces? Should PoE be used?
Training and support
The more complex the access software is, the more urgent it will become to obtain comprehensive training on how to deploy and maintain the system. If you decide on an easy-to-use software like Kisi, you will actually cut down your overall training costs. During the migration, the support provided by the software provider is crucial for running an optimized system. Simply put, an easy-to-deploy solution will require less dependence on the software provider's support team.
Conclusion
If your workplace is still using traditional cards or fobs with an on-premise access control system, it’s likely time to consider migrating. Traditional credentials look pretty similar today as they did 20 years ago, but the technology and encryption inside modern cards have evolved significantly to discourage would-be forgeries.
Uncertain if now is the right time to migrate to the cloud? Then ask yourself this question: If you were implementing your access control system for the first time, would you purchase an on-premise solution?
Learn more about the Kisi migration ROI, or check the migration options here.
Save time. Enhance security.
Modernize your access control with remote management and useful integrations.
Continue learning

