What is a Wiegand device? #
A Wiegand device refers to a type of electronic device commonly used in access control systems. It is named after its inventor, John R. Wiegand.
A Wiegand device consists of a card or key fob embedded with a Wiegand wire or coil. The wire is typically made of stainless steel and is surrounded by insulation. When the Wiegand device is brought close to a Wiegand reader, the wire interacts with the reader's magnetic field, generating an electrical pulse. This pulse is then interpreted by the access control system, allowing or denying access based on the information encoded in the device.
Wiegand devices are known for their reliability, durability, and resistance to tampering, making them popular in security systems.
These devices follow a similar basic function that we see in bank cards. However, a bank card will use a band of ferromagnetic material instead of wiring. The wiring in Wiegand devices makes the systems harder to duplicate.
In summary, Wiegand devices are cards and any kind of data reader that operates on a special wire communication system. These need to be used with a Wiegand sensor in order to work.
What is a Wiegand reader? #
A Wiegand reader, or sensor, is used to read the information on a Wiegand device. Some of the information held on these devices include:
- Credit card numbers
- Bank account numbers
- Employee identification information
- Criminal records
- Medical histories
The set of wires that contains this information is incredibly difficult to counterfeit or duplicate. In order for these systems to be utilized, a Wiegand reader will pick up the information found on the device. This is what we call the Wiegand effect.
If you are interested in finding out more about the inner workings of these units, it is best to consult a wiring diagram. Here is a great example of a Wiegand wiring diagram to see in detail how these devices work.
What is 26-bit Wiegand? #
A complete Wiegand system includes the device that holds the data, as well as the reader. The specialized wired format of communication between the reader and access control technology is key here. When dealing with these devices, you will also come across the term “26-bit Wiegand”.
26-bit is the encoding used by the readers and proximity credentials. Basically, this is the protocol of the data found on your Wiegand device. 26-bit is the industry-standard format of open encoding when it comes to access control systems.
The data encoded using this kind of format offers a huge amount of possible facility codes and unique card numbers. This helps to keep your data more secure in the Wiegand system.
What is an HID prox used for? #
HID prox refers to a type of card that is commonly used in access control systems. HID prox cards, or simply HID cards, are used in conjunction with specialized readers. These cards need to be placed within close proximity of the readers to pick up the data and allow for access.
The cards use RFID-embedded technology to make them easy and convenient to use with readers. These are often utilized for opening doors, or on public transport systems.
HID cards use radio frequencies or special microprocessors to work with the reader.
What is the Wiegand effect? #
The Wiegand effect refers to the behavior of magnetic fields that comes from the specially designed wiring of the above-mentioned systems. This effect occurs when a Wiegand device is placed in contact with a Wiegand reader.
It produces a nonlinear magnetic effect generated in this specially annealed wire. The kind of wire used in a Weigand system is important here. This wire is a low-carbon Vicalloy. It is a ferromagnetic alloy of cobalt, iron, and vanadium.
When you use an ID card or access control device to open a security door, for example, the Wiegand effect is taking place. It is this magnetic effect between the wiring and reader that makes your device work.
Migrating from Wiegand to the cloud with Kisi’s Wiegand board #
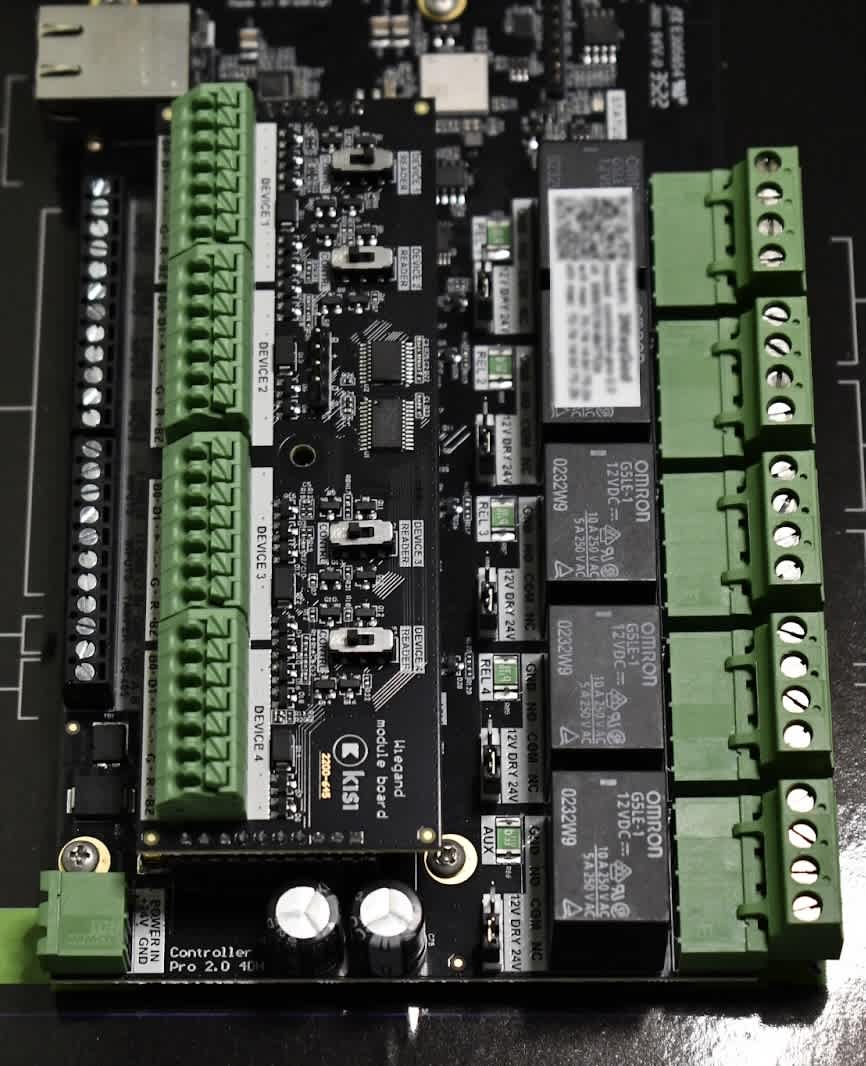
You can easily upgrade your on-premise Wiegand devices to enjoy cloud-based access control with Kisi. The Wiegand Board is an add-on board to the Kisi Controller Pro 2 that enables you to connect legacy Wiegand-enabled hardware, such as HID readers, pin pads, and QR readers, to the Kisi system. It has four interfaces, supporting up to four legacy hardware devices.
Watch the video below for more info.
Why use the Wiegand board? #
- Enjoy the benefits of the Kisi system without the costs of replacing your existing readers
- Added support for legacy hardware, such as Wiegand-enabled readers and pin pads or control panels
- Expand the scope of Kisi’s access control to more products beyond the Kisi system
Benefits of the Wiegand board #
- Seamless transition into the Kisi environment with existing setups that use legacy Wiegand-enabled hardware
- Minimizes cost, since old hardware and wiring do not need to be replaced
- Opens up access to the Kisi experience, including the mobile app and the web dashboard. Enjoy remote unlocks with the Kisi app or by using existing legacy credentials.
Inputs and outputs of Kisi’s Wiegand board #
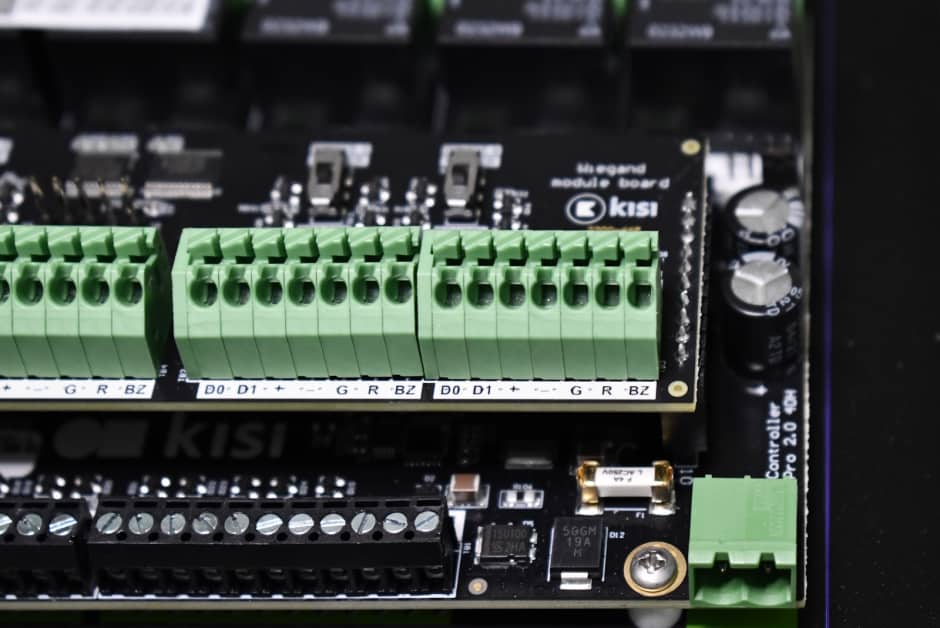
The Wiegand board contains four different interfaces with seven ports and a switch on each interface. The green headers connect to the wires of Wiegand-enabled hardware and allow for communication between the Wiegand board and legacy hardware devices.
Input
D0
D1
+
-
G
R
BZ
Switch
Definition
Data line 0
Data line 1
12 Volts direct current
Ground
Green LED
Red LED
Buzzer
Switches the interface between a reader or a controller
How to install Kisi’s Wiegand board #
Required components
- Kisi Controller Pro 2
- Kisi Wiegand board
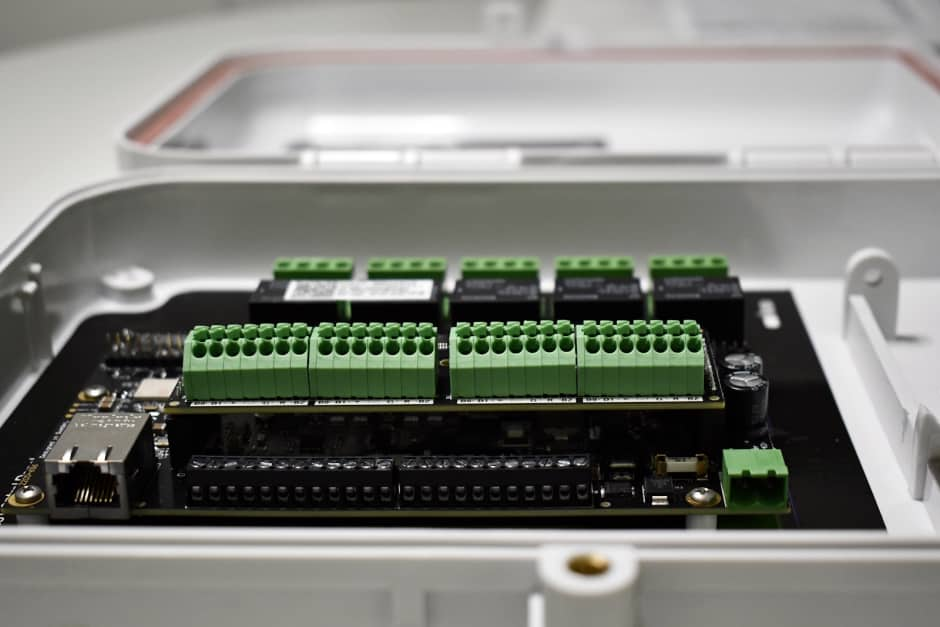
Connecting the Wiegand board
- Unplug power to the Kisi Controller Pro 2 before wiring.
- Identify the black connectors on the Kisi Controller Pro 2 located on the top and bottom of the left side of the board.
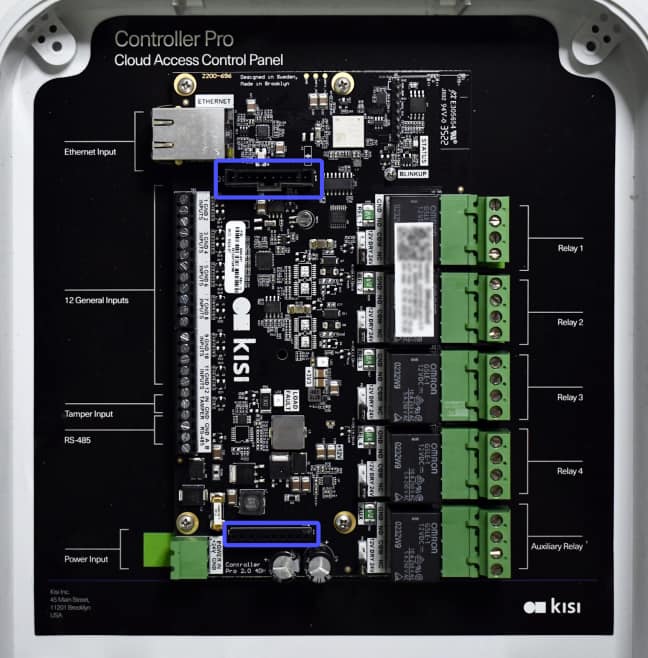
- Align the connectors on the back of the Wiegand board with those on the controller. Ensure that the orientation is correct by aligning male pins to corresponding female pins.
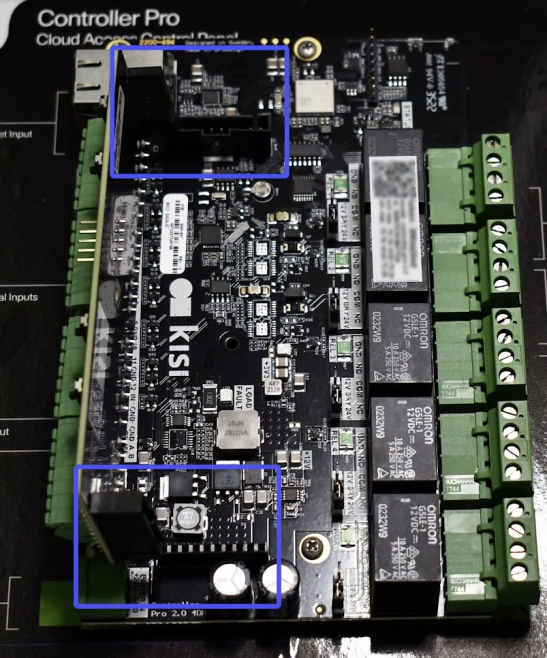
- Firmly press the Wiegand Board into place.
- Reconnect power to the Kisi Controller Pro 2.
Wiring a Wiegand-enabled reader
- Select one of the four Wiegand channels on the Wiegand board.
- Toggle the switch of the selected Wiegand interface to READER mode.
- Connect the keypad reader's D0 wire to the D0 port of the Wiegand channel (Green - Data line 0).
- Connect the keypad reader's D1 wire to the D1 port of the Wiegand channel (White - Data line 1).
- Connect the keypad reader's + wire to the + port of the Wiegand channel (Red - 12 volts direct current).
- Connect the keypad reader's - wire to the - port of the Wiegand channel (Black - Ground).
Wiring a Wiegand-Enabled Controller
- Select one of the four Wiegand channels on the Wiegand board.
- Toggle the switch of the selected Wiegand interface to CONTRL mode.
- Connect the controller's D0 wire to the D0 port of the Wiegand channel (Green - Data line 0).
- Connect the controller’s D1 wire to the D1 port of the Wiegand channel (White - Data line 1).
- Connect the controller's + wire to the + port of the Wiegand channel (Red - 12 volts direct current).
- Connect the controller's - wire to the - port of the Wiegand channel (Black - Ground).
Get more from your Wiegand access control by migrating to Kisi #
Kisi allows for a cost-efficient upgrade to cloud-based security. Move your access control system to the cloud without investing in all new hardware, wiring, or contractors. You get to keep your standard Wiegand readers while enjoying Kisi’s intuitive dashboard. Download our ROI document to learn more.

