In this article, we’ll discuss the scourge of modern offices: internet outages, and how they affect your day-to-day operations. We’ll go through some stats on internet outages, and explore some causes and solutions to these. Later, we’ll look at how internet loss affects access control, and what future innovations can help solve these issues.
How bad is losing your internet, really?
As it turns out, internet outages are pretty common, even for the big guys. If you don’t buy it, check out this article by CRN on the 10 biggest power outages of 2018. It includes all the biggest cloud service providers. With the tech industry and most offices so reliant on the internet these days, you really start to wonder how bad an internet outage actually is.
Pretty Bad, As It Turns Out
Yep, losing your internet is bad, even for a short amount of time. In this article you’ll see research by Cisco showing that just an hour of internet downtime can cost a small to medium-sized business anywhere from about $8,500 to about $70,000. That’s a lot of variance, and that’s because there’s also a lot of variance in the size and internet dependence of businesses, but regardless that’s a lot of money!
Losing internet, for most of us, means a full stop in productivity. Coders can’t use Github to push and pull code, sales people can’t make calls, with most phones operating over the internet these days, and marketing can’t communicate effectively. And even when the internet connection is restored, it often takes some time to refocus and get back to normal productivity levels . If you’re in any sort of flow state, any interruption can completely derail you, making it difficult to get back to the same state of mind.
What causes an internet outage?
There are many reasons the internet can go out in your office. From natural disaster to human tampering, to power surges, and more. We’ll cover the two most common ones here.
Power Outage
The internet needs electricity to run, so if the power goes out, so will the internet, generally speaking. For a more detailed explanation of power outages, procedures, and how they affect access control, check out [this article (POWER OUTAGES ARTICLE)].
Faulty Internet Router
If the cause isn’t related to the power, then it could be related to the internet router or modem itself (unless it’s your computer!) The first thing to try is the old “turn it off and back on again” technique, and if that still doesn’t work, then check out this handy WikiHow article on troubleshooting a dead network, and take steps to ensure that it doesn’t happen again!
ISP Shutdowns
Failing the other options, your outage could be the result of a whole internet service provider shut down. This happens more often than you’d think, with every major network provider experiencing a shutdown approximately once every 16 months. There’s not much you can do to restore the internet if this happens, but happily, there are ways to not leave yourself vulnerable in these situations.
How to Avoid an Internet Outage
Before moving on to access control-related topics, we’ll briefly cover a few ways to avoid an internet outage, so that this problem doesn’t even get the chance to rear its ugly head.
Redundant Internet Providers
This is essentially just what it sounds like: a second (or even third) internet provider with a router set up in your office. If your primary internet provider shuts out for any reason, you can just switch over to the redundant one.
This is particularly useful in the case of a router/model failure, or an issue with the network provider. If the power goes out, and you don’t have backup power, then both networks will go out. However, if there are issues with only one of the networks, you can ensure that you’ll still be covered with a redundant connection.
Different Types of Internet
Similar to the redundant internet providers, you might want to look into redundant ways of getting internet to your employees, even if it’s from the same provider. And I’m not just talking about wireless versus ethernet: there are different ways of getting the signal to your office, with the main ones being fiber internet (notable: Google Fiber) and microwave internet.
Sometimes, if the internet cuts out and it’s an issue with the router or modem, the same provider can still supply you with internet, but the means of providing it needs to be different. This is where redundancy comes in handy. By using multiple methods of wiring your machines directly to the ISP, you bypass the issue of router error and get continuous internet.
What happens to access control when the internet goes out?
We’ve covered causes of internet outages and ways to avoid it, and now we can take a look at access control specifically, and how a power outage affects your access control.
Why does internet matter for access control?
At first glance, you might wonder why you even need the internet for the proper functioning of access control. If you have a key to the lock, that should be enough! Thankfully, access control has evolved way past the old, clunky, and unreliable lock and keys, and towards IP-based smart cards and fully mobile solutions, like Kisi’s.
The advantages of these fully mobile systems are huge, and we encourage you to check out [this other article (LINK TO MOBILE UNLOCKS ARTICLE)] where we describe them. The one drawback, however, is that they are reliant on power to function, and on the internet to be able to communicate with the cloud servers.
While this makes the connection more secure and makes the process much more intuitive, it does mean that you’ll have to consider what will happen when the internet goes out. We’ll explore the procedures in place right now!
Ensuring a Safe Exit
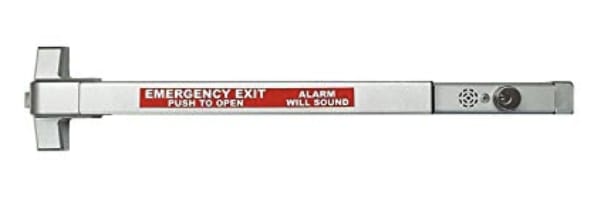
When installing an access control system, the first requirement that any good provider and installer will be sure to have is a safe and accessible exit path, that cannot be compromised by things like power or internet outages. This is actually a fire safety law in every state, and if your office has locks that wouldn’t normally allow this, you will have some sort of panic push bar installed on your door.
With exit strategies assured, we can now turn our attention to entering the space, and how that’s affected by internet outages.
Backup Means of Entering
As a first line of defense, with better access systems like Kisi, in every installation, there will always be an alternate analog method of opening doors. While we prefer promoting a mobile-first interface, we understand that unforeseen complications can pop up, so adding this as an alternative worst-case-scenario method won’t hurt! Note: The analog method will be installed on the door locks, not on the access control readers themselves.
Other than that, there are more sophisticated, IP ways of ensuring access. As long as the power is up, the readers and access controllers are still technically functioning. So while they cannot communicate with the home servers, they can still communicate locally via Bluetooth and NFC. As long as they have a log stored showing who is allowed access, they can authenticate phones and credentials on the spot. This is called caching, and we’ll explore it in the next section.
What does the future look like for offline access control?
While some businesses and functions rely entirely on cloud-based solutions, access control is one of those that can’t afford to have any downtime, and musto have a backup for those cases when the internet or power cuts out.
Local Information Caching: What is it?
Caching (pronounced “cash-ing”) is a term used for locally storing information from a larger database. As an example, if you download something off the internet onto your computer, you are technically caching it, though that’s not really the main use of the term.
The term is mainly used when there is a large database that a machine needs to constantly pull information from, and as a shortcut, it locally stores the information that it accesses most often . This way, it saves time and resources by not having to put in a request to the server every time it needs that information. It also has the added bonus that connectivity to the server isn’t required in order to access that cached information.
How does local caching help with access control?
For access control, as for many other industries, the future seems to be heading towards a hybrid model with cloud-based servers, and decentralized local hosting. The first part isn’t new: most of the best access control systems host the data on their servers. However, to ensure that functionality remains when offline, some data needs to be cached on the local controllers themselves: This is decentralized local hosting.
This makes the solution more robust, as every location isn’t totally dependant on communication with the servers, and as long as the vulnerabilities and IP security concerns can be ironed out, it’s a completely viable and optimal solution. With this architecture, you can cache your own location’s access credentials log on your controller, so that anyone who was allowed access can enter even without internet, then the system will sync back up as soon as connectivity is restored.
Closing Thoughts
Losing internet in your facility is never good: It hampers productivity and can cost businesses thousands of dollars. This is especially true with access control, where a loss of internet means a much less smooth and intuitive access experience. But there are ways to prevent internet outages, and with innovations in decentralized hosting and caching, there are sophisticated workarounds as well.
Save time. Enhance security.
Modernize your access control with remote management and useful integrations.

