Role-based security is a particularly effective safety strategy for big organizations with a large number of users and systems that have an increased risk of leaking sensitive information.
How Role-based Access Control Works #
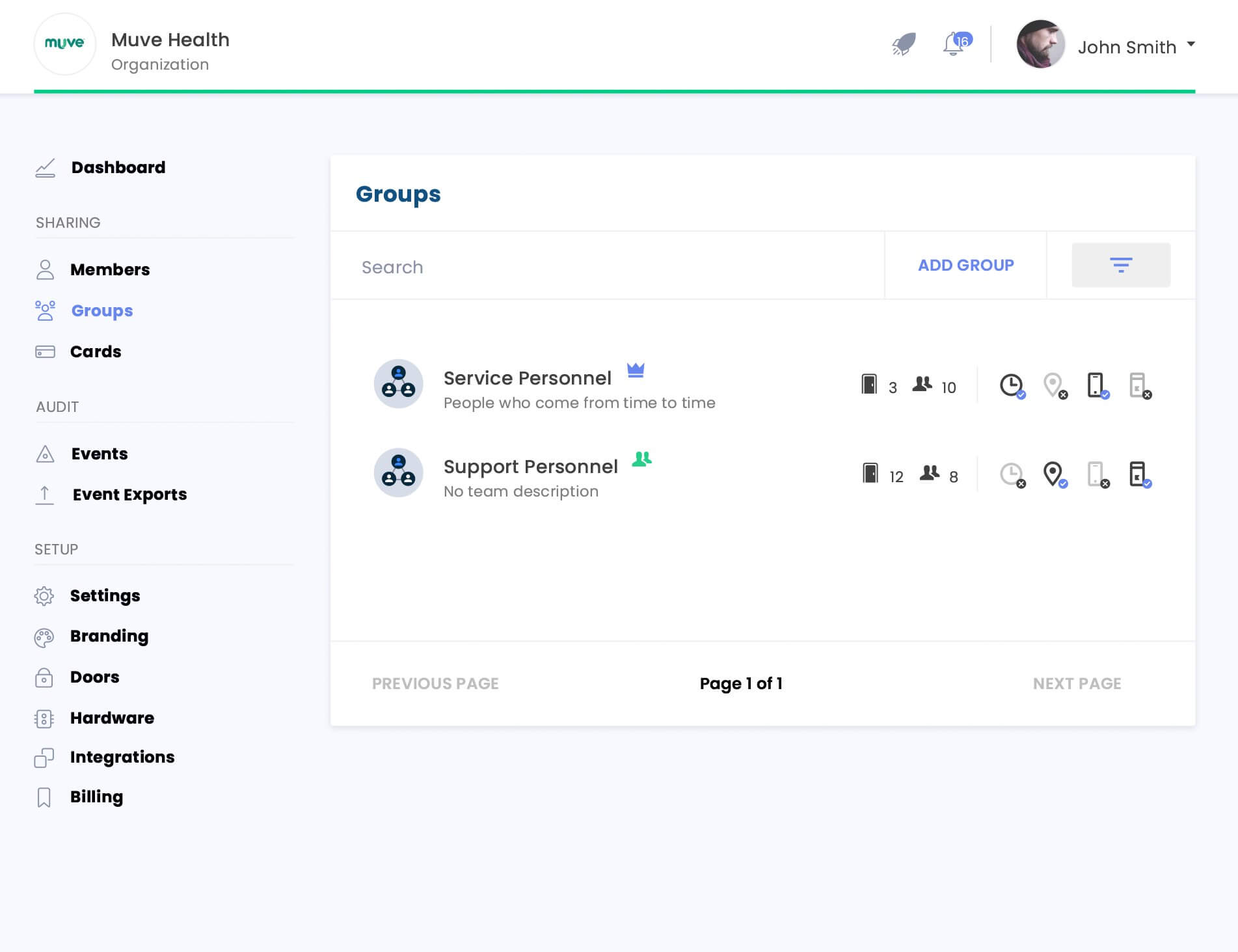
RBAC naturally fits into a company that analyzes its security needs and job duties, where employees are grouped into roles according to their function within an organization, and the roles are aligned with access permissions.
Users with the same roles have identical access rights. This is very useful for companies with a large number of personnel performing the same duties, i.e. accountants, insurance agents, healthcare personnel, customer support personnel, etc.
Here are some examples of role-based access control: A department manager has any permissions associated with his role (viewing and editing contracts, access to reports, a database of clients, certain applications, etc.) while an assistant’s role-based privileges will be limited compared to the ones of the chief manager. An accounting clerk will not have access to the same files and databases as a CFO, etc.
Benefits of Role-Based Access Control #
This security strategy has a number of benefits including:
- It is solid. Companies can easily control users’ access based on their roles.
- It improves operational performance. Thanks to RBAC many transactions are automated, and employees don’t waste time using the applications and services that are not needed for fulfilling their responsibilities.
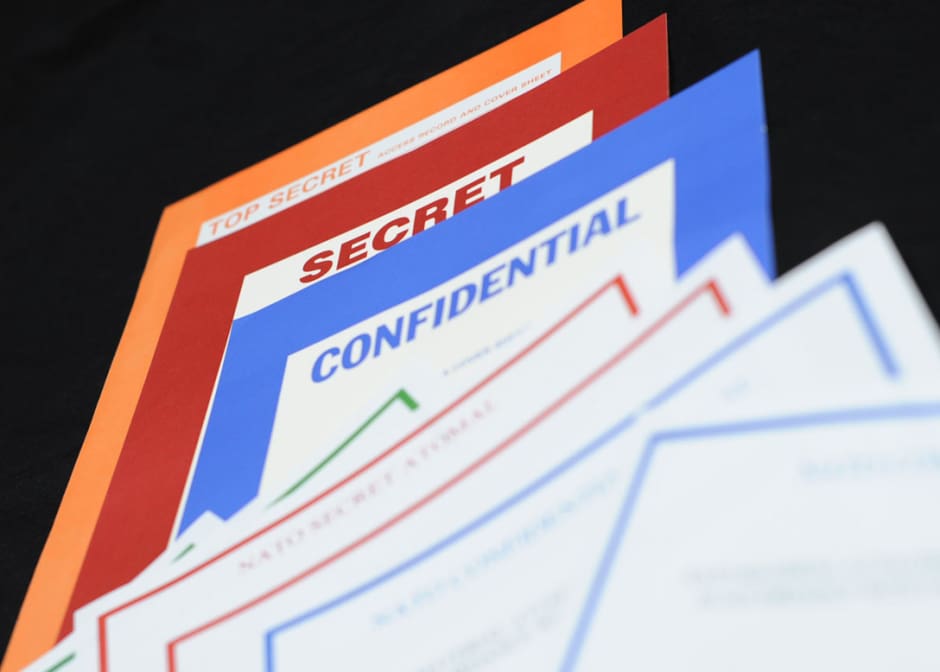
- It decreases a risk of security breaches and data leakage because only a few people within an organization have access to sensitive data.
- Scalability. As a company grows and more employees are hired, the number of roles do not necessarily have to change. This makes it easier for the HR and IT departments, which otherwise would need to perform a number of administrative tasks.
- Better security compliance. Having RBAC implemented means that a company meets requirements as far as privacy and confidentiality are concerned.
To sum it up, implementation of role-based access control and its continuous enhancement has a number of advantages from protecting sensitive data to streamlining processes within an organization with a number of users performing the same duties.
Best Practices for Implementing Role-Based Access Control #
Role-based access control best practices can be achieved following these steps:
- Define data and resources to which access should be limited
- Create roles with the same access needs
- Avoid creating too many roles as in this case you will defeat the purposed and run a risk of creating a user-based access control instead of RBAC
- Align the roles with employees within your organization
- Analyze how roles can be altered and how new employees can be registered and old accounts terminated
- Ensure a company-wide RBAC that is integrated across all systems
- Organize employee training so that the staff members are aware of the RBAC principles
- Conduct audit to ensure that everything is followed through as planned