Many modern companies have multiple offices in different locations, yet not enough IT managers to go around (sometimes even only one IT manager for every location). You will generally see an IT manager in the headquarters or main office, while satellite and sales offices might not have a dedicated one. This raises many issues, not the least of which is the need to manage the IT infrastructure remotely. In this article, we’ll cover that topic, and focus on how multi-location remote access control can help alleviate this problem.
When You Should Manage IT Remotely
With the smart office taking over traditional analog systems, all of the systems you’re likely to have in your office will have some sort of network capability. Whether they have Bluetooth, RFID chips, or have WiFi connectivity, they will have some method of communicating wirelessly with other devices.
Given the high connectivity of all the systems related to IT, you could easily network them all together and manage the system remotely. But why should you? Wouldn’t this expose you to network vulnerabilities? Actually, no: sometimes remote management might be the only choice available for lone IT workers, or people who need to coordinate with other IT managers across locations. In these cases, remote management is a must.. Beyond security measures, managing IT remotely presents many advantages.
Being able to handle crises at home or on the road after hours can be insanely beneficial in case of an emergency.
Setting up a VLAN
For a secure network, it’s often recommended to set up a VLAN, or virtual local access network. For more information on these, check out this helpful link. Essentially, this will create a protected network for all of the devices connected to it via Ethernet cable or wireless network. All of these are connected to a single switch on a local network, and that switch is then connected to the cloud.
Rather than having to secure your network for all your devices, you can just purchase a VLAN switch with built-in protections. This way, you know that your entire local network, and all devices connected to it, will be safe from online attacks.
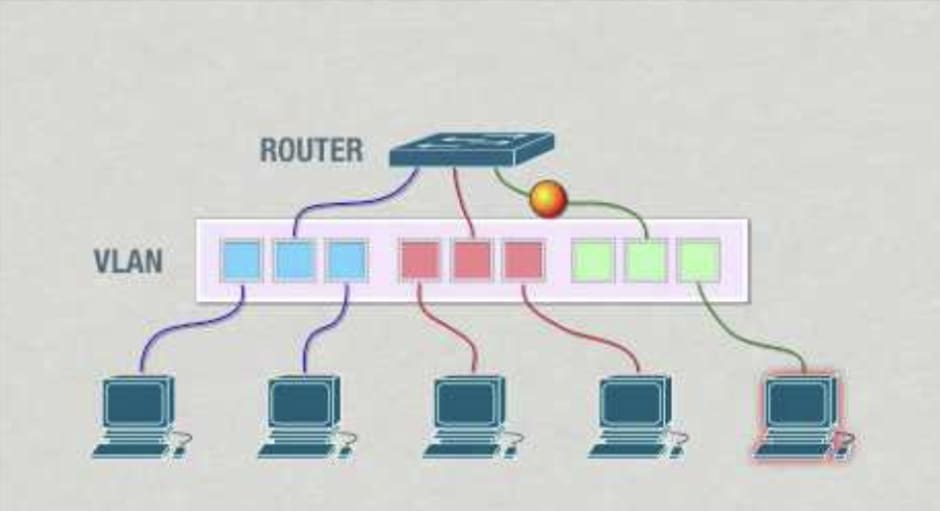
(Representation of how a VLAN protects your devices from any harmful IP traffic)
You can also control a VLAN remotely: Given that the switch is connected to a network or cloud that you have access to, you can monitor it all from a remote interface. The power of VLANs is that any networked device can be connected to one.
Remote Monitoring Access Control
With modern system like Kisi you actually have remote capabilities set up in the controllers and readers themselves: The controllers are connected to the Kisi cloud. With this, you can control the controllers and readers all from the Kisi interface. However, if you want to also monitor their infrastructure, and ensure that they are working properly, you can connect them to a VLAN.
An added advantage here is that you can connect all of the controllers in your space to a single switch, provided you have one powerful enough. A Kisi controller can manage up to four doors, the ideal number of doors for one abstract “space,” but you may want to see the network health of all your controllers on one interface, and you can accomplish this with a VLAN.
Additionally, you don’t need to connect the devices themselves to the network. The VLAN creates a local network to which they all connect, reducing the vulnerability of your system, and giving you a failsafe in case the network is weak or goes out in one part of your office.
Once all this is set up, happy managing! You can review the particulars of multi-door and multi-location access control with the Kisi cloud interface at this link.
Closing Thoughts
Remote IT management isn’t just an advantage these days, in some cases, it’s a necessity. With the proliferation of satellite offices and multi-location interconnected networks, the power of VLANs is a huge asset, and connecting your access control infrastructure to them ensures that you can constantly monitor the status of your physical security, even remotely.
Save time. Enhance security.
Modernize your access control with remote management and useful integrations.

