Creating a proactive plan to resolve infrequently, sometimes recurring events not only reduces the amount of time spent responding to “urgent tasks,” but also increases efficiency and compliance by establishing a process for handling such events.
In this lesson, we’ll take a closer look at the most common manual tasks administrators have to respond to during weekends or off-hours and how Kisi can be leveraged to prevent or eliminate them.
Topic 1: Office Closure (Vacation) Functionality
Office closures can happen predictably every year, in the event of vacations, or unexpectedly due to emergency maintenance, construction, etc. Creating a plan for how you respond to these closures will ensure your location is secured quickly.
Typical types of office closures:
- Public holidays
- Health incidents (e.g. Covid 19)
- Annual off-site
- Emergency maintenance or construction
Even if the office is closed via Kisi during those times, as an administrator you can still unlock the door remotely for delivery or cleaning staff.
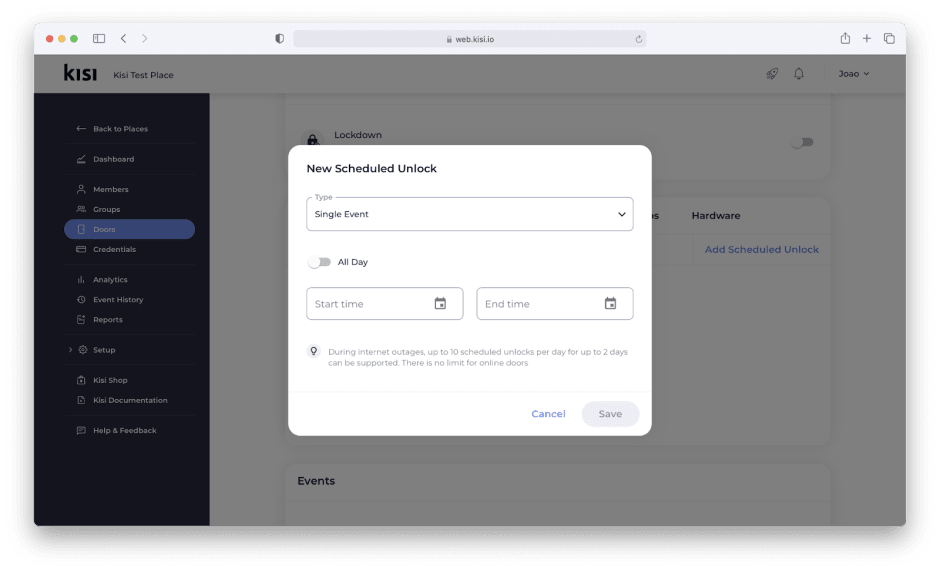
Disable Unlock Schedules
Unlock schedules can be useful in keeping publicly accessible spaces unlocked for a set duration (eg, business operating hours) to allow clients, vendors, or visitors access to the spaces you permit.
Scheduled unlocks should be modified to accommodate for public holidays, disabled temporarily, or deleted completely when they are no longer needed.
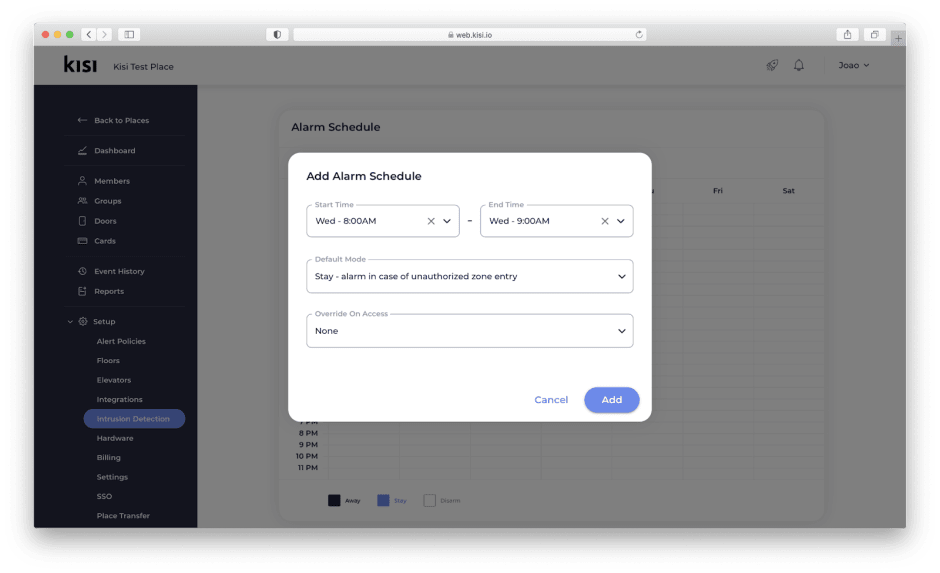
Override Unlock Schedules with Intrusion Detection
Intrusion Detection’s default and optional override modes add an additional layer of security over your access control solution. With Intrusion Detection, administrators can override scheduled unlocks for public holidays. Once the zones have been created and doors assigned, the administrator can set them to “away” for the day (e.g. January 1st). Then, door schedules won’t be activated unless overrides are allowed.
This solution requires door contact sensors to be installed at the door and connected to Kisi.
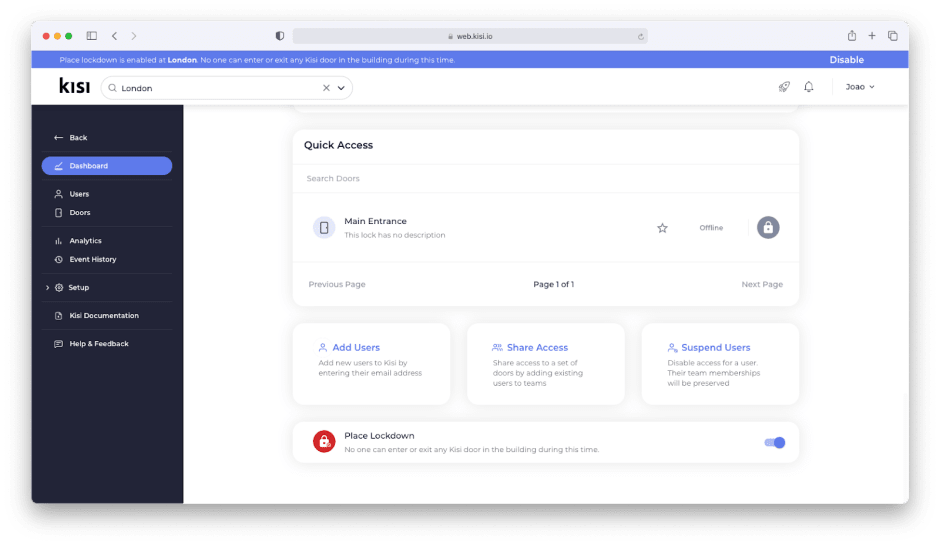
Activate Lockdown
In an emergency situation, being able to quickly perform a remotely activated lockdown is important. Kisi allows administrators to perform lockdowns by door or place. During a place lockdown, all doors are secured and no one is allowed to enter the facility. Door lockdowns behave the same as a place lockdown but only for the specified door.
Suspend Access
If you don’t want to remove someones’ access right but temporarily “suspend” them from being able to access the office, use the “suspend access” functionality in Kisi.
When activated, the user keeps their original access rights, but can’t use them until access is “unsuspended”. This feature is often used for a certain group that needs to quarantine or for desk booking. In the event of booking, everyone will be suspended by default and only activated when they reserve a seat.

Topic 2: Member Management
Defining a process related to user management, including member onboarding and offboarding, is not only an administrative time saver but can eliminate many of the issues the undefined process introduces.
Automate onboarding and offboarding
Incorporating access control onboarding and offboarding into your existing process ensures that access is granted every time a new member is onboarded and revoked when they are offboarded.
Kisi can be configured to integrate with supported CRM, directory, or SSO providers. For more information about creating a custom integration, please refer to our integration API documentation.
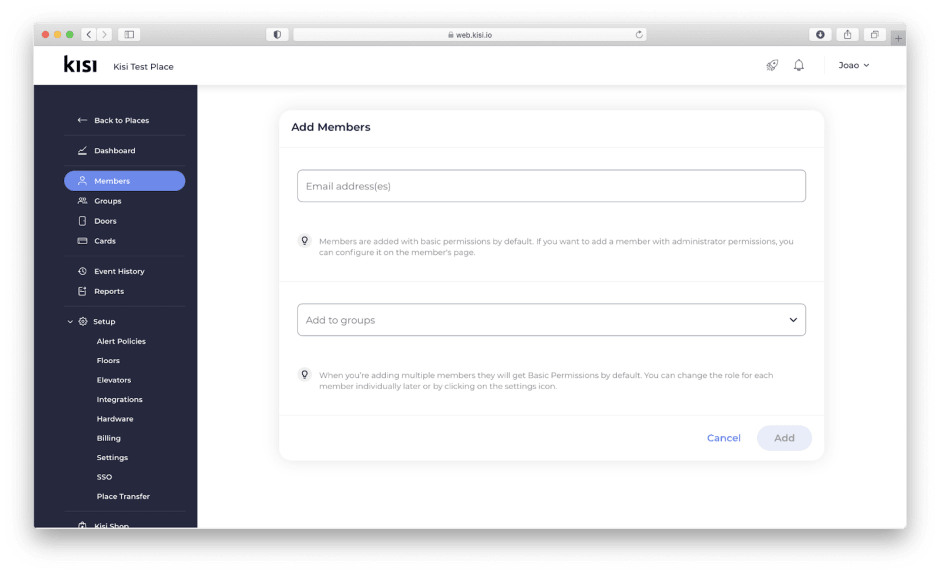
Manually add or remove users
If you don’t wish to add or remove members through integrations, it is recommended that access control onboarding and offboarding be added to your current onboarding/offboarding process.
In smaller organizations, it can be feasible for the Organization Owner or Administrator to manually provision and revoke access for all users. As an organization scales, it often makes more sense to utilize Organizations Managers and Team Administrators to complete the onboarding and offboarding of Kisi members for their team.
Mobile member onboarding is simple and easy, requiring only the user's email address and group assignment.
Offboarding is even quicker, from the user menu click the trash can icon next to the user and their access will be revoked for your place immediately. For users with physical credentials, these can be unassigned directly from the user’s profile.
Review user- and facility activity
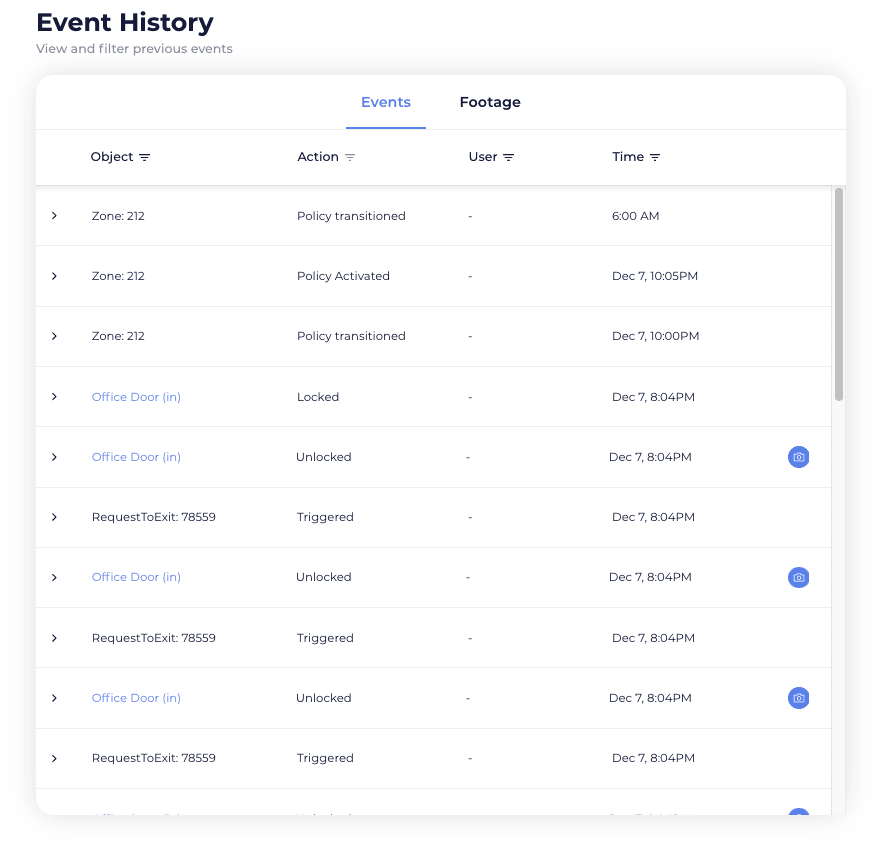
User activity can be quickly accessed and reviewed by any Kisi administrator or manager through the user's profile. To view a specific user's0 recent activity, type their name in the user search, select the appropriate user and navigate to Events.
Topic 3: Lost Credentials
Lost credentials cost an organization time, money, and can lead to a compromised access control solution. Creating a lost credential response plan and educating your team on how they can assist your administrators is key to reducing the amount of time spent addressing missing credentials, thereby freeing your administrators for more important activities.
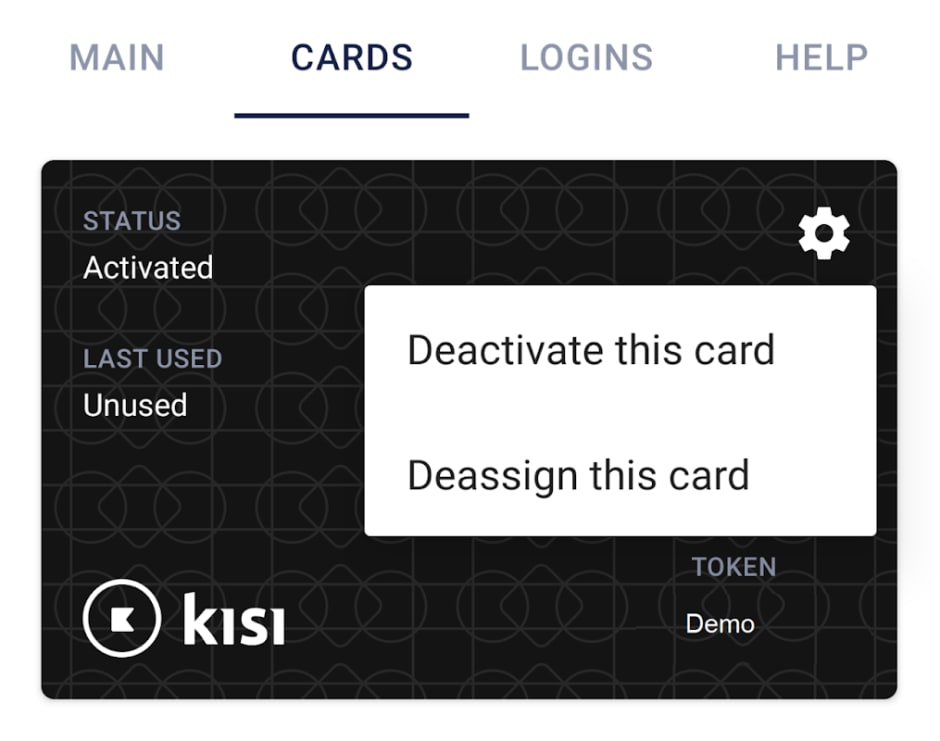
Disable Credentials: Self-Service
Kisi allows end-users the ability to deactivate their own physical credentials directly from the mobile- or web app. Users can navigate to settings, select cards to see the physical credentials associated with their profile and deactivate the missing credentials. It is recommended the user notify their administrator if new credentials are required to be provided by the organization.
This can be an incredible time-saver: Imagine someone losing their wallet at a bar on Saturday night including their access card. The user can immediately self-service deactivate their credential and does not have to embarrassingly ping IT in the middle of the night and wait for a resolution.
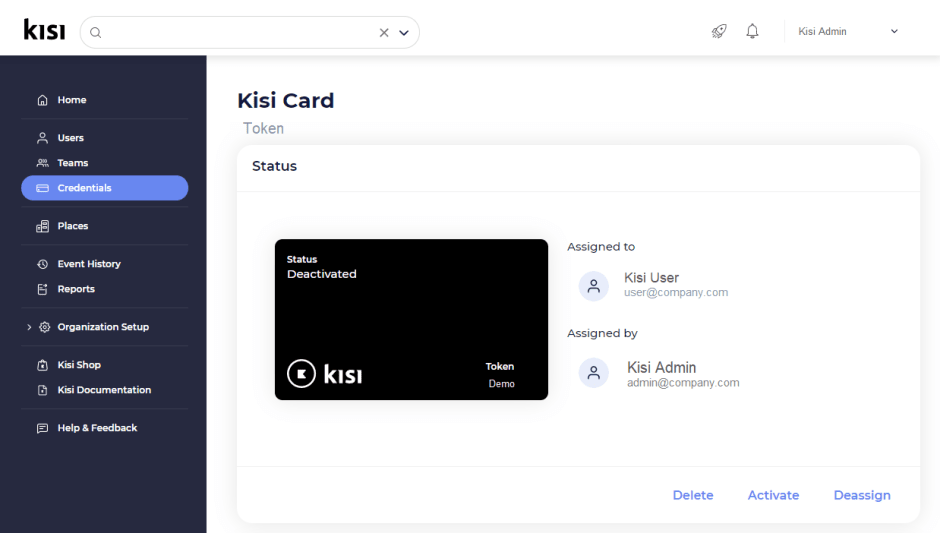
Disable Credentials: Administrator
In the event users are unable to deactivate their credentials, administrators can quickly deactivate credentials from the user's profile or by searching for the credential token (if known). If the user has other credential types, these will not be impacted unless they are also reported lost/missing.
Credentials Audit
It is recommended that administrators audit user credentials when completing user audits. To audit user credentials, navigate to Reports from the Kisi web dashboard and select User Exports before clicking New Export. The downloaded file will share the last time each user accessed your spaces using various credential types including physical credentials, quick access link, or mobile app.
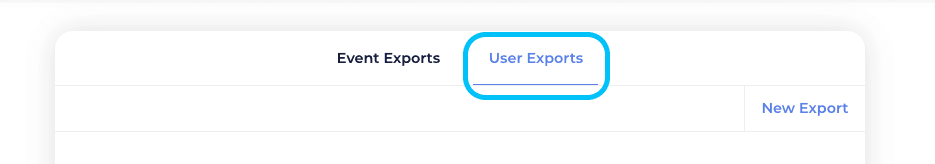
Another method administrators can employ to determine which credentials are assigned but not being used by their organization is to view them from the Credentials menu. Users who have activated their physical credentials will have a green checkmark next to their credential record.

Topic 4: Stay in control remotely
As a cloud-based access control solution, Kisi gives administrators more freedom to administer Kisi wherever they choose from any internet-enabled location globally. Kisi also allows for administrators to be notified in real-time when specific events occur via email or push notification.
Setting common alerts
When you create an alert policy, you will be required to define the conditions necessary to trigger a notification.
After-hours alert - A weekend or after-hours alert policy could be configured to apply to all the doors of your place and trigger a push notification when any of them are opened by any user during the hours you define as after hours.
Sensitive door alert- A sensitive door alert policy could be configured to trigger a notification when doors at your place are forced or left open.
Intrusion detection
Intrusion detection allows you to create alarm schedules for zones within your place. When a zone enters a policy-violated state, notifications are sent to chosen recipients and, if installed and integrated, an alarm siren is triggered.
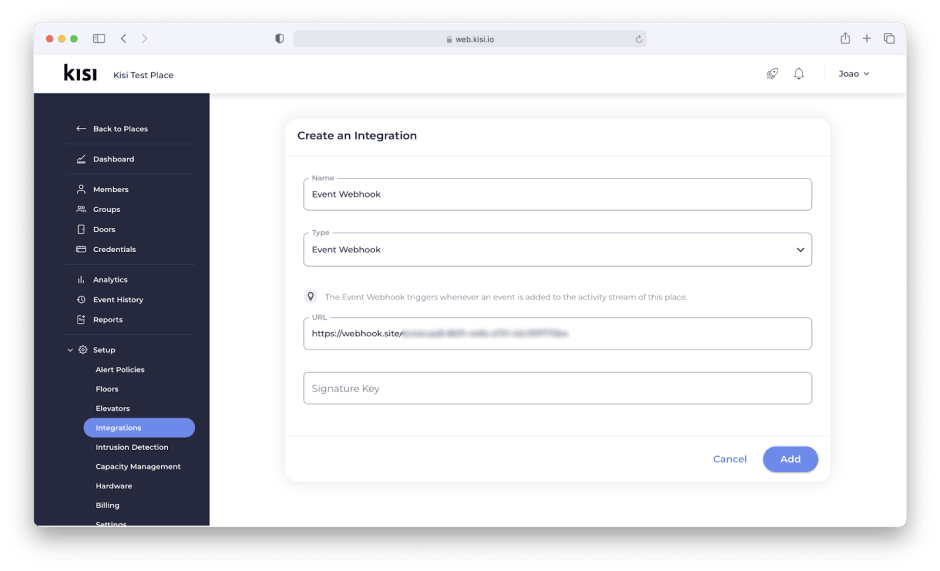
Event webhooks
Leverage event webhooks to push events directly to other monitoring or reporting services you employ. Once the integration is configured, any activities from the events stream will forward to the webhook integration.
Topic 5: Redundancy setup
Creating redundancies in your access control setup can reduce downtime and establish systems that work more reliably.
Backup Credentials
Users can be credentialed with up to 2 physical credentials in addition to their mobile app. This allows users the flexibility to use the credential which is most convenient or available to them.
Users can also manage their own physical credentials from the Kisi dashboard. In the event they lose one of their physical credentials, they can deactivate it themselves immediately.
Redundant Connectivity
Kisi Readers are designed to perform unlocks leveraging several communication channels including BLE, NFC, and mobile unlocks. When the internet isn’t available, users can still perform unlocks from their mobile app by transmitting the unlock request via Bluetooth.
Kisi Readers can be set up with both POE and WiFi. By setting both connections, your reader will automatically transition to the secondary connection should the primary fail. Another feature of the Reader Pro is Offline Mode. Offline Mode leverages a user's cellular data to transmit unlocks when an internet connection is unable to be established.

Since Kisi’s devices are typically connected to an IT rack, it is safe to assume that the IT rack itself has been set up with additional redundancies, but this is always worth verifying with your internal teams.
Backup Power
As part of redundancy planning, it is important to understand what happens in the event of a power failure as your Kisi devices and electric locks will not work without a primary or backup power source.
Kisi device power - In most cases, Kisi devices are connected to the UPC of the IT system, or to a normal power outlet in buildings where a backup power generator is available.
Lock power- Locks are often wired to a backup battery power supply that delivers around 24 hours of additional power. This means that doors will stay in the position they are in during normal operation.
Topic 6: Fire Alarms
While the Kisi Controller does not have a Fire Alarm Control Panel (FACP), it will work with any off-the-shelf alarm panel, e.g. the Bosch FPA-1000 Fire Alarm Panel, which is often already installed in buildings.
When the fire alarm is tripped, it will send a signal to the power supply and interrupt the fire relay control—this allows your doors to remain unlocked from the outside while power is removed (fail-safe) during an emergency. This functionality is independent of Kisi and works regardless of any connectivity issue with your Kisi controller.
If you’re installing the FACP yourself and looking to connect your magnetic or fail-safe strike locks to your own fire alarm, Kisi recommends introducing an external power supply to provide power to your locks as well as providing a built-in FACP. The external power supply and fire alarm panel combination that Kisi recommends is the Altronix AL600ULACM.
Save time. Enhance security.
Modernize your access control with remote management and useful integrations.
Continue learning

