Pin pads or keypads can be used in various scenarios. You can use them as standalone pin pads, keypads on door locks or on deadbolts, as IP-connected pin pads, or you can connect them to a central access control system. Some businesses use them to track time and attendance by pairing them with biometrics, since PIN codes can be too easily shared.
With Kisi, you have various options for upgrading your existing keypad readers and adding necessary functionalities, like remote, centralized management, and two-factor authentication (2FA). Contact our team for a solution tailored to your existing hardware and needs.
What is a keypad or pin pad? #
Keypads are one of the most common forms of access control today. A keypad is a set of buttons complete with all digits (0-9). When using the basic keypad reader, users simply input the correct pin, and the door unlocks. This is an entry-level form of security. Your spaces are more secure, but people can easily share pin codes with others, which poses a security risk.

While the look of the keypad has mostly stayed the same since its invention in the 1960s, its functionality has widely expanded. With a system like Kisi, your legacy keypads can become part of a new, future-proof setup to upgrade your security. Explore more on this cost-efficient upgrade to cloud-based security with zero downtime in our ROI document, or explore the migration options.
Watch the video below for more information on keypad readers, their benefits, use cases, and installation tips.
Keypads for doors and access control #
The basic legacy keypads are not a secure solution to make an office safe, only a convenient method to gain access. They are very easy to install, and most people have experience using them.
While a keypad is a keyless solution, the key or PIN can be shared an infinite number of times between people, regardless of authorization or permission levels. Basing your security on trusting users with confidential information is risky for many businesses.
It’s also challenging to hold anyone accountable should a security breach occur, especially if the PIN information is shared across a large number of users. To increase security, most businesses shifted to digital and mobile access cards.
Keypads are still an easy way to bring beginner-level security to a previously unsecured place. They’re great for places like shared restrooms, so you can quickly give access to anyone while retaining certain control of the space. They are also a good secondary option for already secured doors in case something goes wrong.
Keypad access control: PIN and Proximity readers #

Most modern businesses with electronic locks use a keypad either as a secondary access option alongside another security access control system or as a stand-alone access point (usually for backroom storage). The ease of installation also makes it a very common accessory for electronic locks. Sometimes the keypad is integrated with another security system, like a card reader, or inbuilt with fingerprint scanners on each button.
Some blue-collar and industrial work environments use PIN pads for time and attendance tracking. This use-case makes it especially vulnerable to passing the PIN code to coworkers who badge you in.
With Kisi, you can migrate to the cloud and upgrade basic keypad reader functionalities with a straightforward installation process.
Installing a keypad reader for access control #
Be sure to unplug the controller before wiring anything. To integrate your electric strike lock with Kisi, you need:
- Kisi Controller Pro 2
- Kisi Wiegand board
- Keypad (Wiegand-compatible)
- Small flathead screwdriver
Hardware setup: Wiring the keypad
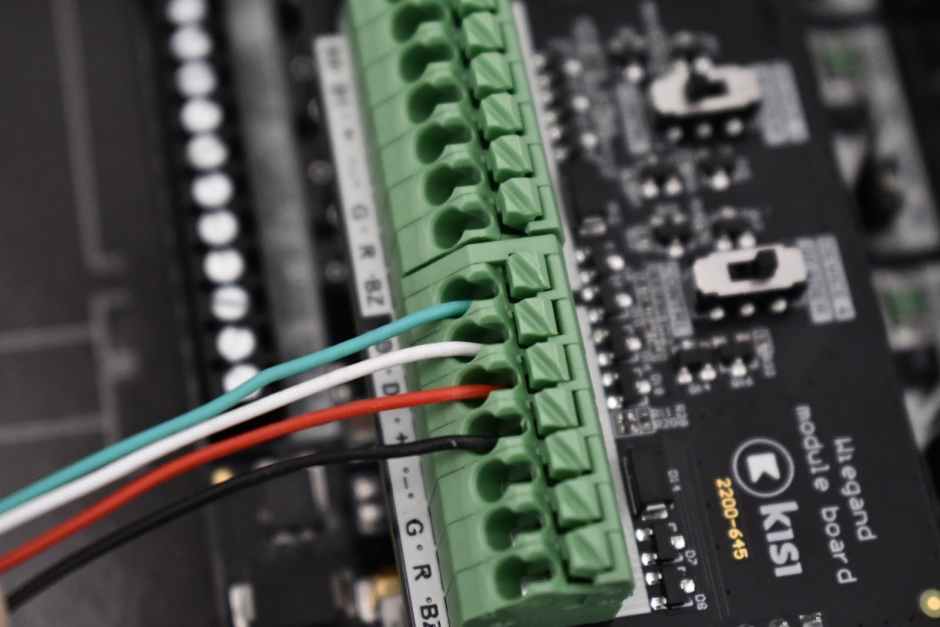
- Ensure the controller is unplugged.
- Attach the Wiegand board to the controller.
- Wire the keypad to the Wiegand board, connecting the D0, D1, +/12V, and -/GND ports.
- Ensure that the switch on the Wiegand board where you have connected the keypad is set to ‘Reader’.
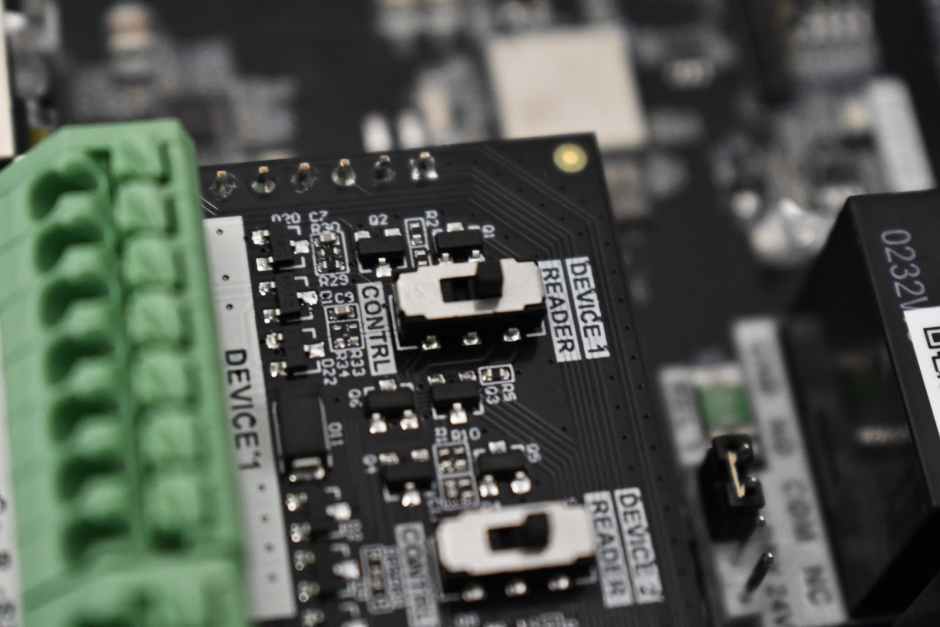
Once you’re done with the wiring, the installation should look similar to the images below.

Software setup #
- Go to web.kisi.io.
- Click on ‘Places’ and select your place.
- Click on ‘Hardware’, ‘Controllers’, and select your controller.
- Scroll down and choose the Wiegand channel that corresponds to the reader that has been connected to the system.
- Click on ‘Type’ and select ‘Legacy Keypad Reader’.
- Click on ‘Keypad Type’ and select a format that works with your keypad. Kisi supports five types of keypads: Single key Rosslare format (Wiegand 6-bit), single key Nibbles complemented (Wiegand 8-bit), four keys binary + facility code (Wiegand 26-bit), one to five keys binary + facility code (Wiegand 26-bit), single key (Wiegand 4-bit).
- Click on ‘Search door or elevator’ and enter the door to unlock with the keypad.
- Toggle’ Master Code’ on, and select a code for your keypad.
- If you want to require a pin and a physical credential like a card, toggle’ Two-Factor Authentication’ on. Tip: This is a much more secure option. If someone finds out the pin, they still won’t be able to unlock the door.
- Click on ‘Save’.
Keypad lock on door #

Standalone door lock pin pads are an entry-level access control choice. These locks don’t need to be connected to a centralized access control system to operate, making them a convenient and cost-effective solution. Businesses often use it to convert a single, uncontrollable point of entry to a locked door in a fast, efficient, and cost-effective way.
Keypads on door locks might be most familiar in public spaces or venues. Many businesses use keypads to safeguard restrooms and other facilities, which require a code for use.
Standalone PIN #

Standalone PIN pads typically come in a flush mount, single-gang, design that is easy to install in drywall, or single-gang electrical boxes. They typically can support different types of PINs between 1 and 6-digit codes. However, one of the biggest vulnerabilities is the ability to change the codes by entering the master code.
PIN pads can be a great addition to electric access systems to serve as a backup in case something goes wrong. That way, no one needs to know the PIN code.
Bring additional functionalities to your keypad readers #
Leverage your existing keypad access system with Kisi’s backward compatibility to bring all your locations to the cloud. Upgrading to Kisi enables you to mix and match keypad usage with mobile credentials, and manage all locations and users centrally. You can also set up two-factor authentication, requiring non-frequent users to scan their credentials and enter a PIN for an additional layer of security.
For multi-site solutions, this option allows for hybrid deployments across any existing door setup, including both door and elevator keypad readers. By connecting your existing readers and cables to Kisi, you can use a phased approach to stay on budget and choose which parts of your current access system you’ll keep. Our cloud-based system allows you to set different access levels for various users and groups.
Unlock unlimited scalability by transitioning to a modern, cloud-based access control system. Explore our unique migration journeys tailored to your specific needs. Get in touch to find the right migration path for you and experience fast and easy installation for a seamless and cost-efficient upgrade.

