Causes of Physical Security Breaches #
Unauthorized access may be gained by an outsider as well as by an in-house employee. Both physical access to a building by a stranger or entry to a server room by a staff member with no permission are examples of unauthorized physical access. Although a security system may have various loopholes, most commonly unauthorized access is gained thanks to:
- Tailgating – i.e. an act when unauthorized people follow through a door someone who has an access card
- Weak doors that can be easily levered or broke in through
- Smart cards which can be easily hacked
- Lost or stolen keys
- Portable devices such as laptops, mobile phones and USB drives
- Unlocked server room doors
- Insider threat, etc.
Any of the above mentioned loopholes create security gaps which can be taken advantage of. Because of an unauthorized access companies may be subjected to physical theft of devices and equipment, compromise of electronic information, identity theft and vandalism. What’s more, human lives can be endangered too. Therefore, it is important that a company addresses any of the existing loopholes and prevents possible threats.
First and foremost, you need to define how unauthorized access can occur at your company and develop a program aimed at eradicating any possible loopholes.
Different levels of security are crucial to prevent unauthorized access . Robust access control system, employee control and emergency response help prevent unsanctioned access to facilities, devices and information.
- Begin with perimeter security. Make sure you use fences, gates, guards and video surveillance around the perimeter.
- By installing motion detectors and alarm systems you can attain an additional level of security.
- Implement identification cards to verify people entering the premises, including visitors, contractors and personnel.
- Lock up areas with sensitive information. It is also advised to enforce delay control on server room doors. Check out our guide for server room requirements.
- Conduct background check of employees before onboarding. "Onboarding" is the process of integrating a new employee into an organization, training and orienting them.
- Make sure you have a new hire forms checklist thanks to which you can verify your new employee’s work eligibility.
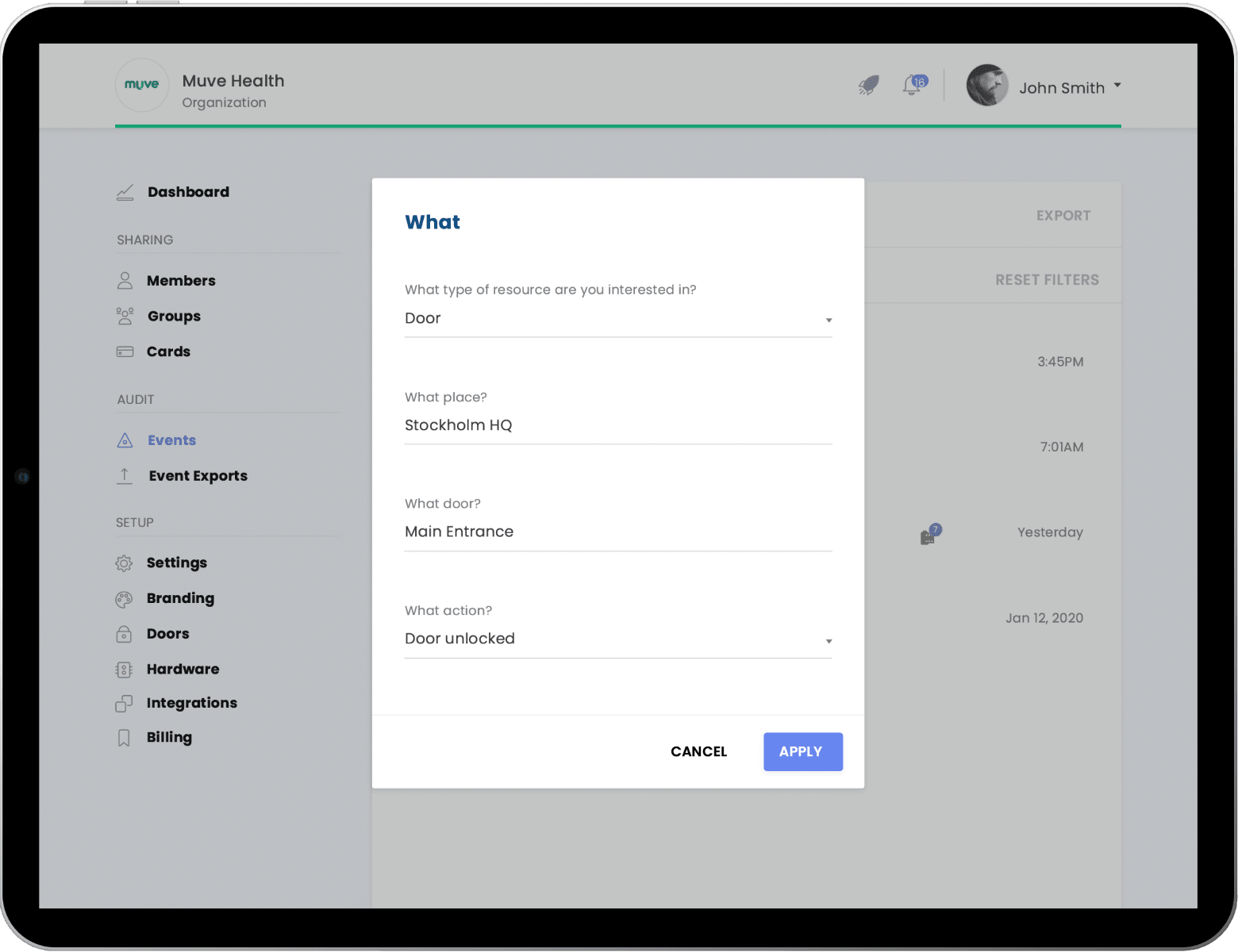
- Set up different access control levels. Each employee should be granted permission to enter facilities depending on their role within an organization.
- Use cable locks for computers in order to prevent theft of electronic devices.
Desktop locks are aimed at protecting computer equipment from theft.
- Lock up sensitive files or USB drives in safes or drawers.
- Develop an emergency plan and train employees to troubleshoot possible security issues and inform of any suspicious behavior they notice.
It is important to remember that security starts at a physical level. By implementing measures aimed at preventing unauthorized access you can protect your assets, information and personnel from internal and external security threats which otherwise might have a detrimental impact on your business.

