What security tools do modern workplaces use? Are there IoT office solutions that can help modernize traditional security approaches? How do these smart office tools work with the IT stack? We’ll tackle these and many more questions in this article.
Why is office security important?
The FBI reports one robbery every 1.6 minutes, one burglary every 18 seconds, and even one property crime every 4 seconds. Even though the numbers speak for themselves, you might want to make office security a priority for your own peace of mind and to protect your career as well..
If you are responsible for securing a modern office, you might feel overloaded, confused, or simply frustrated when conducting your research. If you are like us you’ll want to make your office secure while at the same time enhancing the culture and aesthetics of your space. At least that’s how we felt in companies we’ve worked at before.
That’s why we compiled the latest and greatest smart office technology in the security industry in one overview, as well as a more extended description of more traditional choices open to you beyond the IoT to secure your office.
Before we dive into the overview, let’s look at the single categories of security system components that businesses use, as well as a quick summary of where the industry is currently.
Industry Overview
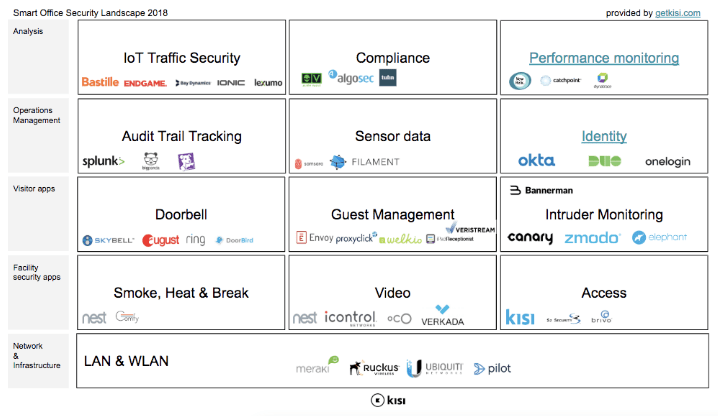
The entire office security system runs on your network and wireless infrastructure which builds the foundation. On top of that, facility security apps like smoke, heat and break-in detectors as well as access control and video make sure you have proper security controls within your facility. When it comes to visitor management, most companies add doorbells, visitor management software, and intruder monitoring like audio sensors or motion detectors. Once all the apps are in place, you can start running IT operations management on top of the existing systems and data to make it easier to navigate for your operations staff. On a monitoring and analysis level, you can then run traffic security, compliance and performance monitoring software to ensure macro-level functionality. This layer is the most established and standardized since it’s already being used by many of the cyber applications but still not connected to many of the office locations.
Generally it seems that there are vast amounts of providers both on the network and infrastructure layer as well as the analysis layer. On the other hand, when it comes to the classic office security applications, the market is mostly divided among the existing legacy providers and new entrants from the home automation field.
To help clarify this confusing landscape, we’ve compiled a smart office overview chart outlining the major subfields and notable players in each field. This chart is not meant to be exhaustive but should give you a strong idea of the overall structure of the industry. We will delve more deeply into which companies occupy each space in the overview that follows.
Download the chart as pdf here.
We’ll start the overview with a quick review of IoT traffic analysis and audit trail tools, but won’t go too in-depth as these are typically general SaaS tools with limited customer-facing applications — not necessarily specific to office security. If this is too specific feel free to skip this part and go right into the visitor layer:
Security Analysis Tools
Platforms like Catchpoint provide real-time performance analytics monitoring to track your network’s performance and keep you constantly updated on anything you should be aware of. On the infrastructure management side, you need software to manage network layer firewalls, routers, switches, load balancers, and other network security devices. We can divide this up into two main categories, as follows. For compliance and threat management there are platforms like Alien Vault with built-in security controls for organizations to address compliance and threat management needs. IoT traffic security is monitored by services like Bastille, Bay Dynamics or Endgame.
However, you should not rely completely on the software alone—you will need staff to coordinate operations and take over should any issues arise. IT operations management apps allow you to optimize this process, making sure you’re working on the right issues at the right time.
IT Operations Management
Automate and scale incident management—get rid of those annoying IT alert noises by centralizing and normalizing all of your monitoring alerts from any system with software like Big Panda, Splunk or Datadog to remove any unnecessary distractions. Use Filament or Samsara to pull sensor data from legacy infrastructure: operate without existing cellular or WiFi networks, and instead deploy a private mesh LPWA network using LoRa radios. Connect, scale, manage and orchestrate in real-time all your applications and IoT devices with providers like PubNub.
Now, we arrive at true office security IoT apps — software and hardware that you can install and leverage to increase the physical security of your space while not compromising its aesthetic appeal.
Visitor Management
We will begin with visitor management. Presumably, you will at some point receive visitors into your office — no company is an island! The following tools will ensure that only welcome guests are able to access your space, and help you prevent any mishaps and unwanted intruders.
Let’s start with the first layer of security at most doors — the unheralded and criminally underrated doorbell. Modern doorbells are so much more than a simple chime that sounds around the house — apps like Ring and Doorbird let you control your doorbell and door camera straight from your smartphone. If you want a more complete system with dial pad and intercom function, it would likely be best to look at emerging IP or cellular enabled door entry systems. Once we’re past the front door, you’ll want some sort of system in place to manage guests, identify approved visitors by letting them register in your system, and print ID badges for easier identification. Tools like Envoy, Proxyclick, Welkio, and SwipedOn provide complete functionality right on your iPad for visitors to register. However, despite all this new security, you might still deem it prudent to invest in some form of intruder monitoring. For this, we recommend companies like Canary, Elephant or Zmodo. In this realm, while IoT provides some interesting solutions, it can still make sense to get good old-fashioned security guards for your next event.
Facility Securing Apps
Finally, we move to the big one — facility security apps. This is a very broad category, ranging from physical alarm systems to video monitoring, to motion sensors. It can seem quite daunting at first glance to figure out exactly what you need for your space. We’ve strived to make this process as straightforward as possible to help you navigate this metaphorical minefield.
Alarm Systems
A good place to begin would be with the traditional alarm system. You’re moving in a new space and you think you need an alarm system. Rather than go through the hassle of doing the research you simply call ADT or some similar company. We see it happen over and over again. The phrase ‘alarm systems’ is often used as a synonym for a combination of motion or contact sensors, video and/or access control. We’ll look into each of those , but suffice to say that we think the better solution might be for you to look into modern companies for each of the individual components rather than a one-size-fits-all traditional system. A burglar alarm might not be exactly what you need, especially given the slew of intruder and visitor management apps covered above. You may want to begin with a fire alarm instead. The Nest smoke and CO2 alarm is a great entry-level IoT product for integrating your fire security. If you want a more traditional door alarm system, here is a basic GE door/window alarm that should accommodate all your needs.
Door access hardware
The first and most obvious entry to your space is the door, and as such, measures should be taken to restrict door access and improve lock security hardware. As it so happens, this is our main area of expertise! We will cover conventional locks, pinpads, and keys — from modern keyfobs and badges to biometrics, and our personal favorite, mobile entry solutions.
- Locks: There are many types of locks that fit on your door and many that don’t. We’d recommend taking a look at one of the blog posts we wrote a while back which breaks down all the different types of electronic locks. When deciding on a lock, always go to a local security integrator to get advice on what type of lock, brand, and configuration to buy — otherwise it will be a big mess.
- Keys: Often, the two mainly used keys are tumbler lock keys or lever lock keys, and some also prefer a master key system. However you should note that any traditional key you make will have the issue of keys being easily copied by an unauthorized person or the annoying hassle having to go to a physical location to make copies for yourself. Most modern offices are turning away from traditional keys and to more modern solutions, outlined in the next few sections.
- Pinpads: Having a pin code handy when you’re not there can be a great emergency backup. Assa Abloy’s DK-12 Securitron is a great, easy-to-use entry-level pinpad.
- Keyfobs and Badges: the most popular tech here is RFID based tokens in the form of cards or badges — read more on how they work here. They usually come with more sophisticated software that allows you to program those tokens according to the level of security clearance that person is assigned. Vendors include Keri Systems and Keyscan.
- Biometrics: While biometrics are gaining in popularity (check out how it works) many companies are hesitant to register fingerprints or facesas they don’t want to appear to be a too controlling or bureaucratic. It is also debatable whether they are really more secure than other types of entry systems, and many people actually use them for logging work hours.
- Mobile door access and entry solutions: Never lose your key, never deal with copying keys or having your key illegally copied, and easily activate or deactivate new or old keys. (nb: we are using the term “key” very loosely here — you can actually use your smartphone or key cards/fobs and don’t need to deal with physical keys anymore!) These are only some benefits of mobile-based credentials which streamline operations, reduce organizational risk and ensure business continuity. A perfect example is our very own solution
Window Access Safety
Beyond mere door security, it often makes sense to secure the windows of the space, especially if you are on the ground floor or near a balcony. This really boils down to three factors: preventing a window glass from breaking, reducing the visibility of the space from outside, and alerting you when something breaks.
Applying a security film to potentially vulnerable windows will greatly reduce the risk of a window breaking and thus prevent “smash and grab” scenarios. 3M’s security films are a good option when it comes to clear films.
To deter would-be burglars, you’ll likely want to limit visibility into your office - Lutron Serena provides home-kit enabled shades.
Finally, if all else fails, you’ll want to know when something actually breaks: check out Doberman Security Ultra Slim Alarms or Bosch's DS1108 that you stick onto the window and will trigger the alarm should that window break.
Video Cameras
On to Video cameras. There are traditionally three different types of video cameras used for surveillance: WiFi-based cameras, DVR cameras, or Ethernet connected surveillance devices, and you can select between any of the three based on the particularities of your office, or you can opt for more modern cloud-based surveillance services.
For WiFi-based cameras, Nest is again a popular provider. However, do keep in mind that these cameras are streaming HD via your WiFi, which might result in significant delays in speed for your computers, depending on the strength of your network. Canary.is “smart cameras” is another good example (we touched on these in the intruder monitoring section).
You generally see more conventional DVR-based cameras at the Deli store, supermarkets or fast food restaurants: usually sold in kits of three to five cameras, these are systems for live monitoring every angle of a space, with the benefit of being able to go back to the DVR storage to look up a certain point in time. Check out Everfocus’s kit on B&H.
Ethernet-based surveillance cameras are most commonly used by enterprises and technology companies as you can run real-time analytics on top of the data stream in your Security Operations Center (SOC). Here you’ll find all the big names from Samsung or Sony.
Finally, from the IoT side, we’ve recently seen a few interesting cloud-based surveillance monitoring services (called Video-As-A-Service or VSaaS or VMS). They run ethernet combining the user-friendlyWiFi-based consumer cameras with the professional angle of enterprise lenses. Check out iVideon, Smartvue, Barracuda.
Contact Sensors
Beyond just video, some companies opt for some sort of motion, contact, or presence sensor: There are a plethora of infrared, contact, and motion sensors to detect unwanted intrusions in your space.
Contact sensors are often sold as an “alarm system” like Alarm.com, for example. However these systems just alert you when the door opens and therefore can be prone to to false alarms.
Motion sensors or PIR sensors can alert you when someone moves around your office. However, many modern cameras such as Nest camera or Ring have motion sensors integrated so there is usually no extra need here.
Infrared (IR) sensors: To avoid false alarms, you might want to look into IR beam sensors. Here are some strong choices.
Lighting
Finally we come to lighting, an often undervalued security factor. We recommend hooking up your lights to occupancy sensors such that they turn on when someone enters the space during night times. On the IoT side, Philips Hue lights are probably the most advanced, but Lutron or Leviton might have similar options.
Network and Infrastructure
For all the information you need, and more that you probably didn’t even knew you needed, check our blog post about the right router infrastructure for your office at this link.
Concluding Thoughts
The field of modern IoT office security tools is very rich, and will only increase in sophistication and scope in the future. With modern technologies like access control, real-time performance analytics monitoring, and cloud-based systems, your office can be more secure than ever. Hopefully, this guide has helped get you excited about the industry and has given you an idea of what you might need for your space.
Save time. Enhance security.
Modernize your access control with remote management and useful integrations.
Continue learning

